Ultimate Guide to Security Maturity Models in Healthcare
Post Summary
Healthcare organizations face growing cybersecurity challenges that directly impact patient safety. Security maturity models provide structured frameworks to help these organizations move from reactive threat responses to well-organized risk management. Here's what you need to know:
- What they are: Security maturity models assess and improve cybersecurity practices across people, processes, and technology.
- Why they matter: They help identify gaps, create action plans, and reduce risks, ensuring patient care continuity during cyberattacks.
- Key frameworks: NIST Cybersecurity Framework (CSF), HHS 405(d) Health Industry Cybersecurity Practices (HICP), and tools like Censinet RiskOps™.
- Maturity levels: Organizations evolve from ad-hoc responses (Level 1) to continuous improvement (Level 5), with measurable benefits like cost savings and reduced risks.
These models aren't just about compliance; they're about building resilience to protect patient safety and maintain trust. The full article dives into practical steps, tools, and strategies to assess and improve your organization's security posture.
Common Security Maturity Models for Healthcare
Healthcare organizations have several established frameworks to guide their cybersecurity strategies. These models are designed to help organizations transition from reactive problem-solving to proactive risk management. Among the most widely used in healthcare are the NIST Cybersecurity Framework (CSF), HHS 405(d) Health Industry Cybersecurity Practices (HICP), and the Censinet RiskOps™ platform, which automates these standards. Here's a closer look at how each contributes to building stronger cybersecurity practices.
NIST Cybersecurity Framework (CSF)

The NIST Cybersecurity Framework (CSF) is a well-known tool for structured risk management. It organizes cybersecurity efforts into five core functions: Identify, Protect, Detect, Respond, and Recover. To measure progress, the framework uses four maturity tiers: Partial, Risk-Informed, Repeatable, and Adaptive. These tiers help organizations evolve from inconsistent, reactive responses to fully integrated, proactive operations [4].
- Tier 1 (Partial): Organizations operate without formal policies, leading to fragmented security efforts.
- Tier 4 (Adaptive): Security becomes an integral part of daily operations, using AI-powered analytics and real-time threat intelligence to anticipate and neutralize risks [4].
According to the 2024 Healthcare Cybersecurity Benchmarking Study, co-led by Censinet, KLAS Research, and other key organizations, healthcare providers struggle most with the Identify function. This reflects challenges in fully understanding their asset and data inventories [2].
Ellie Soroush, Senior Security Researcher at Security Compass, highlights the framework's importance:
"The NIST Cybersecurity Framework (CSF) is a widely adopted security framework that helps organizations manage and reduce cybersecurity risks through a structured, risk-based approach." [4]
Additionally, NIST CSF aligns with regulatory standards like HIPAA, ISO 27001, and PCI DSS, simplifying compliance while strengthening defenses [4].
HHS 405(d) Health Industry Cybersecurity Practices (HICP)
The HHS 405(d) Health Industry Cybersecurity Practices (HICP) framework focuses specifically on the healthcare sector's unique challenges. Updated in 2023, it emphasizes "recognized security practices" to address risks like ransomware and vulnerabilities in medical devices [2].
HICP identifies ten key practice areas to address critical risks, including safeguarding electronic health records, securing medical devices, and managing supply chain vulnerabilities. Notably, medical device security ranks as the lowest-performing area, revealing a significant gap in healthcare cybersecurity [2].
The framework also provides detailed guidance for protecting clinical assets like infusion pumps and imaging systems, areas not fully addressed by broader frameworks like NIST CSF [2]. Another weak spot highlighted in the 2024 Benchmarking Study is supply chain risk management, which ranks as the least mature category across all 23 NIST CSF areas [2].
Censinet RiskOps™ and Healthcare Cybersecurity
While frameworks like NIST CSF and HICP offer strategic guidance, healthcare organizations often need tools to put these strategies into action. Censinet RiskOps™ fills this gap by automating risk management processes, enabling organizations to create actionable plans and monitor progress against both NIST and HICP standards [2].
The platform simplifies risk management for patient data, clinical applications, medical devices, and supply chains. Features like automated workflows and real-time risk visualization replace outdated manual processes, making it easier to assess and improve security practices. Benchmarking tools also allow organizations to measure their cybersecurity posture against peer-based standards [2].
The 2024 Benchmarking Study found that stronger CISO leadership correlates with better implementation of NIST CSF and HICP practices, underscoring the importance of leadership in achieving cybersecurity goals [2].
Additionally, Censinet RiskOps™ supports newer frameworks like the NIST AI Risk Management Framework (AI RMF). This is particularly valuable for managing risks tied to AI-powered tools in healthcare. The platform's AI-driven features streamline third-party risk assessments, allowing vendors to complete security questionnaires quickly while summarizing essential documentation. This approach balances automation with human oversight, ensuring effective risk management in complex environments [2].
sbb-itb-535baee
How Maturity Levels Work in Security Models
Security Maturity Levels in Healthcare: From Initial to Optimizing
Overview of Maturity Levels
Maturity levels illustrate how cybersecurity practices evolve from being informal and reactive to becoming structured and continuously improving systems. They serve as a guide for healthcare organizations to evaluate their current security posture and identify steps to strengthen risk management through data-driven strategies.
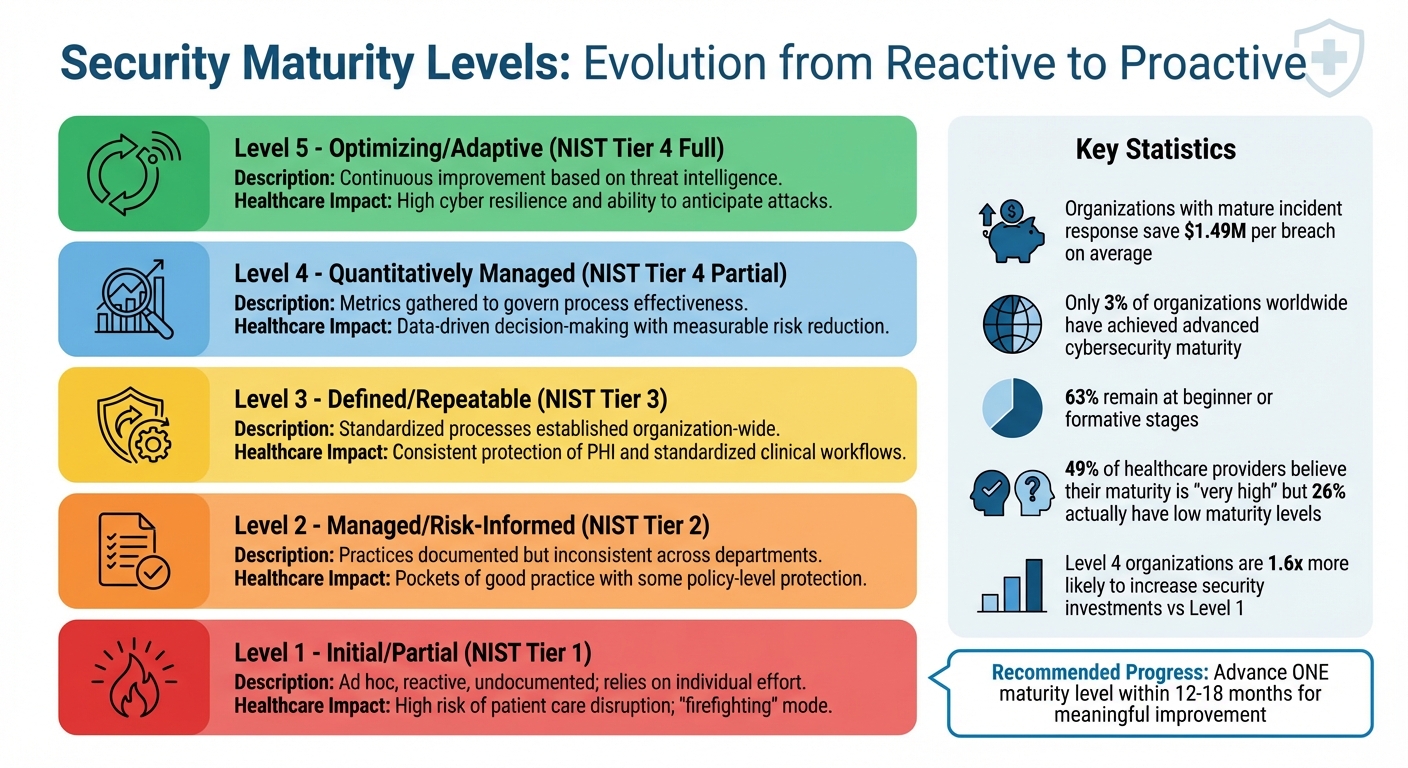
Most traditional models follow a five-level scale: Initial (Level 1), Managed (Level 2), Defined (Level 3), Quantitatively Managed (Level 4), and Optimizing (Level 5)[7]. At Level 1, security efforts are often uncoordinated and depend on individual actions. By Level 5, organizations achieve continuous improvement through techniques like automated monitoring, leveraging threat intelligence, and using predictive analytics[7].
The financial benefits of advancing through these levels are clear. For example, organizations with mature incident response capabilities can save an average of $1.49 million per breach[5]. Despite this, only 3% of organizations worldwide have achieved advanced cybersecurity maturity, while 63% remain at beginner or formative stages[5].
In healthcare, there’s a notable gap between perception and reality. While 49% of healthcare providers believe their cybersecurity maturity is "very high", objective evaluations show that 26% actually have low maturity levels[5]. This disconnect often results in underinvestment in vital areas like medical device security and supply chain risk management. Glenn Baruck captures the stakes well:
Security outcomes are clinical outcomes. A ransomware incident doesn't just encrypt files; it delays lab results, diverts ambulances, and forces staff into paper workflows[1].
Improving maturity levels in healthcare directly impacts patient safety. Higher maturity reduces risks like electronic health record (EHR) downtime, medical device failures, and delays in critical care decisions. Organizations at advanced maturity (Level 4) are also 1.6 times more likely to increase their security investments compared to those at Level 1[5]. Next, we’ll explore how different frameworks assess these maturity levels.
Maturity Level Comparison Across Frameworks
Various models use different methods to measure maturity. For instance, the NIST Cybersecurity Framework (NIST CSF) uses "Tiers" (1–4) to assess the rigor of risk management practices rather than traditional maturity levels[6]. On the other hand, the Secure Controls Framework (SCF) Cybersecurity & Privacy Capability Maturity Model (C|P-CMM) outlines six levels (0–5) with specific criteria for each[6].
| Maturity Level | NIST CSF Tier | Description | Healthcare Impact |
|---|---|---|---|
| Initial / Partial | Tier 1 | Ad hoc, reactive, and undocumented; relies on individual effort | High risk of patient care disruption; "firefighting" mode |
| Managed / Risk-Informed | Tier 2 | Practices are documented but inconsistent across departments | Pockets of good practice with some policy-level protection |
| Defined / Repeatable | Tier 3 | Standardized processes established organization-wide | Consistent protection of PHI and standardized clinical workflows |
| Quantitatively Managed | Tier 4 (Partial) | Metrics are gathered to govern process effectiveness | Data-driven decision-making with measurable risk reduction |
| Optimizing / Adaptive | Tier 4 (Full) | Continuous improvement based on threat intelligence | High cyber resilience and the ability to anticipate attacks |
This comparison underscores the need for tailored approaches to address healthcare-specific risks. The primary distinction between NIST CSF and traditional maturity models lies in their structure. As the SCF Council points out:
The NIST Cybersecurity Framework (NIST CSF) is a popular framework to align an organization's cybersecurity practices. However, one component that is nebulous is the inclusion of Tiers... the reality is NIST CSF does not have a traditional CMM[6].
In simpler terms, NIST CSF Tiers focus on the overall rigor of risk management rather than offering detailed criteria for every control.
For healthcare organizations, progress doesn’t have to mean dramatic overhauls. Setting realistic goals - like advancing one maturity level within 12–18 months - can drive meaningful improvements. Concentrating on high-risk areas and presenting a financial case - such as reduced insurance premiums and breach costs - can help secure executive buy-in[5]. These smaller, targeted steps lay the groundwork for stronger cybersecurity practices in the long term.
How to Assess Your Organization's Security Maturity
Steps for Conducting a Maturity Assessment
Assessing your organization's security maturity begins with a detailed inventory of assets. This means cataloging every system, application, and medical device connected to your network. Why? Because knowing what you’re protecting is the first step to identifying vulnerabilities. Once that’s done, the next step involves using framework-aligned questionnaires, such as those based on HICP or NIST CSF 2.0, to evaluate current practices against established industry standards[10]. These questionnaires should reflect your organization's size and complexity to ensure the assessment captures the actual risk landscape.
Another crucial area to address is vendor risk. Supply chain vulnerabilities are often overlooked, especially in healthcare organizations, where this remains one of the weaker links[8]. Conducting vendor risk reviews includes examining business associate agreements (BAAs), verifying vendor documentation, and ensuring they meet your security requirements. This process gives you a more complete understanding of external risks.
To avoid working in silos, involve cross-functional teams from IT, clinical operations, compliance, and legal departments. Ryan Sanders, CISO at PatientLock, highlights the importance of weaving maturity practices into daily operations to keep up with evolving threats and maintain trust with patients[9].
Tracking findings and their remediation is another key element. Automating this process can help document gaps, assign tasks, and set deadlines for improvements. These steps not only pinpoint risks but also enable actionable strategies to enhance safety. Regular self-assessments, such as annual reviews against updated frameworks like HICP 2023 and NIST CSF 2.0, allow your organization to monitor progress and generate reports that showcase improvements over time[8]. This methodical approach builds a stronger cybersecurity foundation.
Adding automation to manual assessments can make the process even more efficient.
Using Censinet RiskOps™ for Maturity Assessments
Censinet RiskOps™ simplifies the maturity assessment process by automating key tasks. The platform uses tailored HICP-based questionnaires designed to match your organization's size and risk profile[10]. With automated risk scoring, it provides real-time updates as vendor data changes or new threats like Log4j emerge[13]. This eliminates the need for manually tracking risks on spreadsheets.
The platform’s Cybersecurity Data Room™ keeps risk data current and maintains detailed records over time. It also flags critical issues, such as missing BAAs or active exploits, so you can address them promptly[13]. Additionally, Censinet AI helps by summarizing vendor evidence, identifying risks from fourth-party vendors, and generating detailed reports in seconds[11].
One standout feature is peer benchmarking. By leveraging a network of over 50,000 vendors and products, Censinet RiskOps™ allows you to compare your cybersecurity maturity with similar organizations[12]. Executive dashboards offer real-time insights, making it easier to demonstrate compliance during audits and justify security investments to leadership[10].
| Censinet RiskOps™ Assessment Features | Description |
|---|---|
| HICP-based Questionnaires | Designed to identify gaps based on your organization's scale[10] |
| Automated Risk Scoring | Updates in real time as vendor data or threats change[13] |
| Peer Benchmarking | Compares your security posture with industry peers[10] |
| Executive Dashboards | Provides real-time cybersecurity insights for leadership[10] |
| AI Automation | Summarizes evidence and predicts risks in seconds[11] |
How to Improve Your Security Maturity
Creating a Security Improvement Roadmap
Start by using a well-known framework like NIST CSF or HITRUST CSF to measure your current security position and communicate progress. Define the scope by listing systems, medical devices, applications, and patient data storage locations. Don’t forget to identify unsupported legacy systems or third-party connections that could introduce vulnerabilities.
Evaluate your technical, procedural, and organizational readiness. This includes updating outdated devices, securing backups, testing environments, and providing staff training. Assign maturity levels - typically ranging from 1 to 5 - to highlight gaps and track progress. Cybersecurity maturity spans from basic awareness to fully optimized resilience.
Focus on initiatives that address the biggest risks to patient safety and compliance. For example, replace unsupported medical devices, implement multi-factor authentication (MFA), or improve network segmentation between clinical and administrative systems. Regularly validate your security controls through vulnerability scans, penetration tests, and exercises simulating ransomware attacks or data breaches. Store backups in secure, isolated locations and test restoration processes at least twice a year to ensure they work when needed.
Equally important is fostering a security-conscious culture. Create training tailored to specific roles, and run phishing simulations to build awareness. As Baruck explains:
Compliance should be seen as the starting point - not the destination. Many organizations that have suffered breaches were technically 'compliant,' but lacked the maturity to detect and contain threats effectively.[3]
These foundational steps set the stage for continuous and automated improvements, as described below.
Using Censinet RiskOps™ for Continuous Improvement
To bring your roadmap to life, consider using integrated platforms that automate risk management. Censinet RiskOps™ is designed specifically for healthcare organizations, offering tools to support ongoing security maturity. Its AI-powered features speed up risk assessments by allowing vendors to quickly complete security questionnaires, summarizing evidence and documentation, and identifying fourth-party risks. This blend of automation and human oversight ensures efficiency while keeping critical decision-making in the hands of your team.
The platform acts as a central hub for managing AI governance and risk oversight. Key findings and critical tasks are routed to the appropriate stakeholders for review, including members of your AI governance committee. With real-time data presented in an intuitive dashboard, you’ll have a single source of truth for policies, risks, and tasks. This setup ensures accountability and keeps teams focused on addressing the most pressing issues.
Censinet RiskOps™ also promotes collaboration across Governance, Risk, and Compliance (GRC) teams. Its automated workflows and risk visualization tools help healthcare organizations address complex third-party and enterprise risks more efficiently. By combining human oversight with streamlined operations, organizations can align with industry standards while protecting patient safety. This integration ensures that your roadmap milestones are consistently achieved.
Tracking Progress Over Time
Measure your progress using key metrics like reduced vulnerabilities, phishing success rates, backup recovery reliability, and incident response times (MTTD/MTTR). These indicators provide tangible proof of security improvements and help justify further investments to leadership.
Conduct annual assessments and quarterly reviews to stay on top of evolving threats and regulatory updates. Document advancements in measurable terms - for instance, moving from Level 2 (Developing) to Level 3 (Defined) by standardizing processes across the organization.
Use executive dashboards to visualize progress and communicate results to stakeholders. Real-time insights make it easier to demonstrate compliance during audits and show how your efforts enhance patient safety. By consistently tracking these metrics, you can build a strong, data-driven case for cybersecurity investments and strengthen organizational resilience over time.
Conclusion
Security maturity models offer a structured way to protect patient data, ensure compliance, and maintain patient safety. Glenn Baruck emphasizes that security has a direct impact on clinical outcomes, noting how breaches can delay lab results, divert ambulances, and disrupt care continuity [1].
To make the most of these models, organizations should align a standard framework like the NIST Cybersecurity Framework (CSF) with regulatory requirements such as the HIPAA Security Rule [1]. It's crucial to confirm that controls are not only in place but actively functioning. This means assessing electronic health record (EHR) systems, medical devices, telehealth platforms, and third-party vendors. With research showing that only 15% of Health Information System projects succeed fully, while 35% fail outright [14], maturity models help by offering clear roadmaps and measurable milestones. This approach ties back to earlier discussions on structured assessments and continuous monitoring, aligning with frameworks like NIST CSF and HICP.
From these benchmarks, actionable steps should follow. Maturity is an ongoing process, evolving from reactive measures to proactive resilience. Start with straightforward initiatives like multi-factor authentication and endpoint detection. Over time, work toward implementing Zero Trust architectures and continuous monitoring. Engaging clinical staff early ensures security measures enhance, rather than disrupt, patient care workflows.
To secure executive support, present security as a business improvement strategy that aligns with operational goals. Glenn Baruck captures this well: "Leaders fund outcomes, not tools" [1]. Use real-time dashboards and measurable KPIs to demonstrate progress, secure funding, and stay ahead of threats through regular assessments and reviews. Aim for annual formal evaluations and quarterly updates to maintain momentum.
FAQs
Which security maturity model should our healthcare organization start with?
Healthcare organizations should start by using a security maturity model to assess critical areas such as governance, risk management, incident response, and medical device security. A model aligned with the NIST Cybersecurity Framework is a solid choice, as it provides clear stages of maturity, ranging from ad hoc processes to fully integrated systems. These models are designed to highlight vulnerabilities, set a baseline for current practices, and help prioritize the steps needed to improve cybersecurity defenses effectively.
How do we map maturity improvements to HIPAA and audit needs?
Mapping improvements in security maturity to meet HIPAA and audit requirements means leveraging maturity models to pinpoint weaknesses and strengthen compliance efforts. These models allow organizations to evaluate their current security practices, establish clear, measurable goals, and ensure critical controls - like safeguarding electronic protected health information (ePHI) and managing breach responses - align with HIPAA standards. Consistent assessments, along with frameworks such as NIST, play a key role in enabling ongoing monitoring and proactive measures to uphold compliance and stay prepared for audits.
What metrics best prove security maturity gains to executives?
When it comes to proving security maturity to executives, some metrics stand out as particularly impactful. Compliance with industry frameworks like NIST (National Institute of Standards and Technology) and HICP (Health Industry Cybersecurity Practices) is a strong indicator of well-established security practices. These frameworks signal that your organization is adhering to recognized standards.
Other important metrics include:
- Improved cybersecurity benchmark scores: These scores provide a clear picture of how your security measures stack up against industry peers.
- Fewer security incidents: A reduction in breaches or vulnerabilities demonstrates tangible progress in risk management.
- Advancement in maturity levels: Moving to a higher level in security maturity models showcases ongoing improvement.
Additionally, tracking vendor risk assessments and ensuring your asset coverage aligns with established standards can further illustrate your organization's growing resilience and alignment with strategic objectives. These data points not only highlight progress but also help tie security efforts directly to business goals.


